Accelerynt Security Platform
If you run Microsoft 365, this is built for you. Continuous validation that your security controls work as intended, with evidence on demand.
What is true inside and outside your environment right now.
Which controls hold, which drifted, and which fix reduces the most risk.
Evidence you can hand to your board, your auditor, or your insurer.
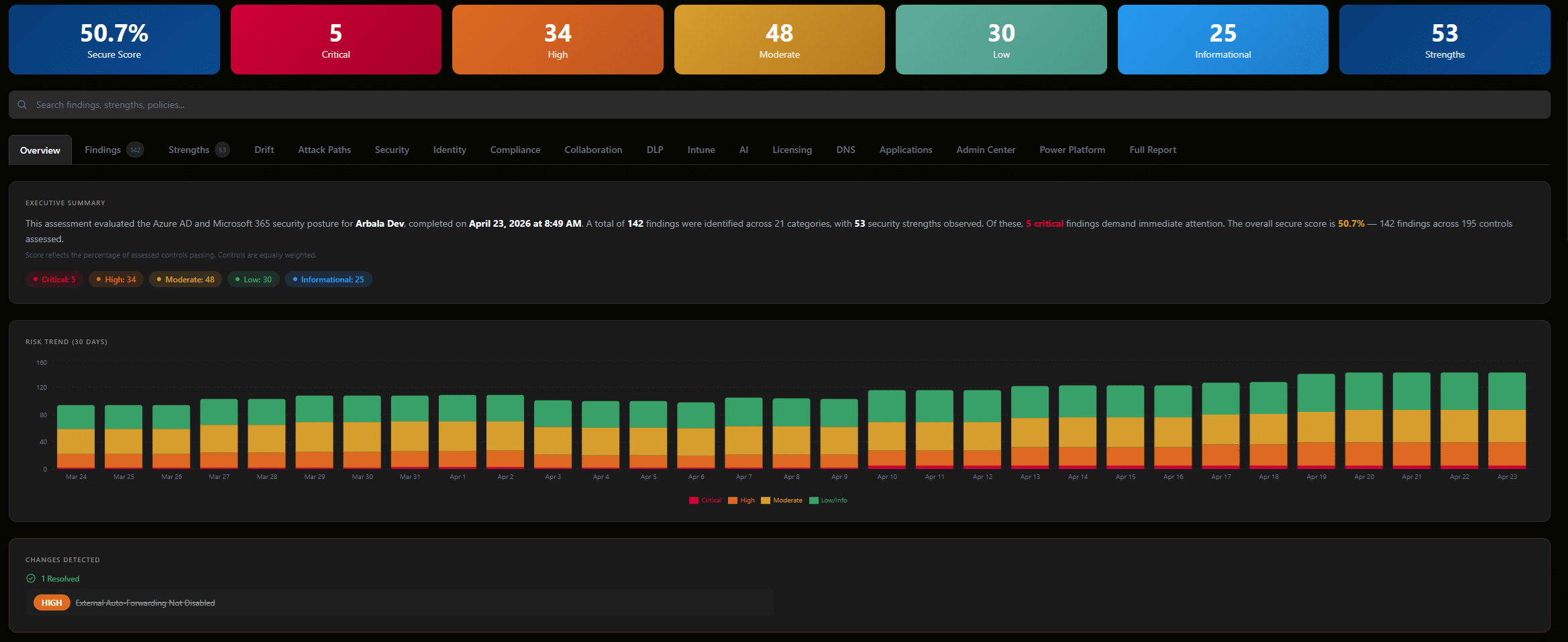
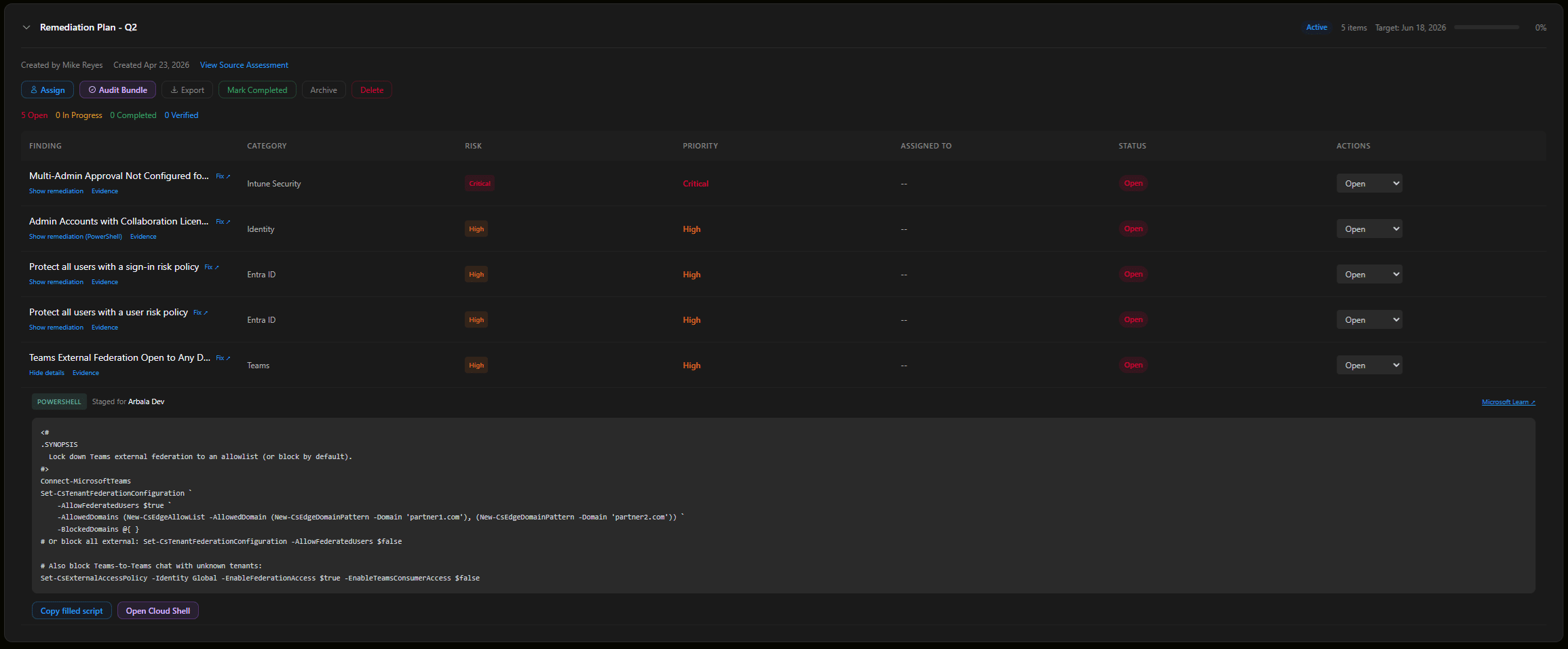
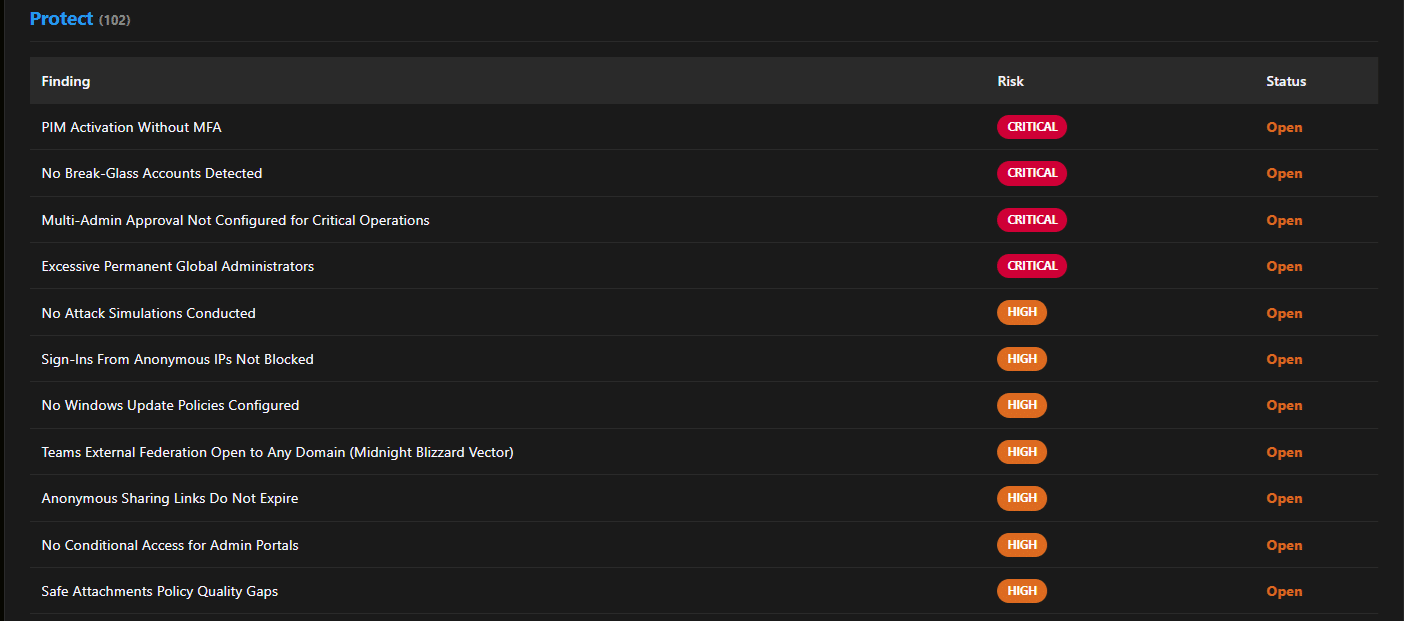
See exactly where you are exposed. Know what needs attention first.
Configuration on the inside. Attack surface on the outside.
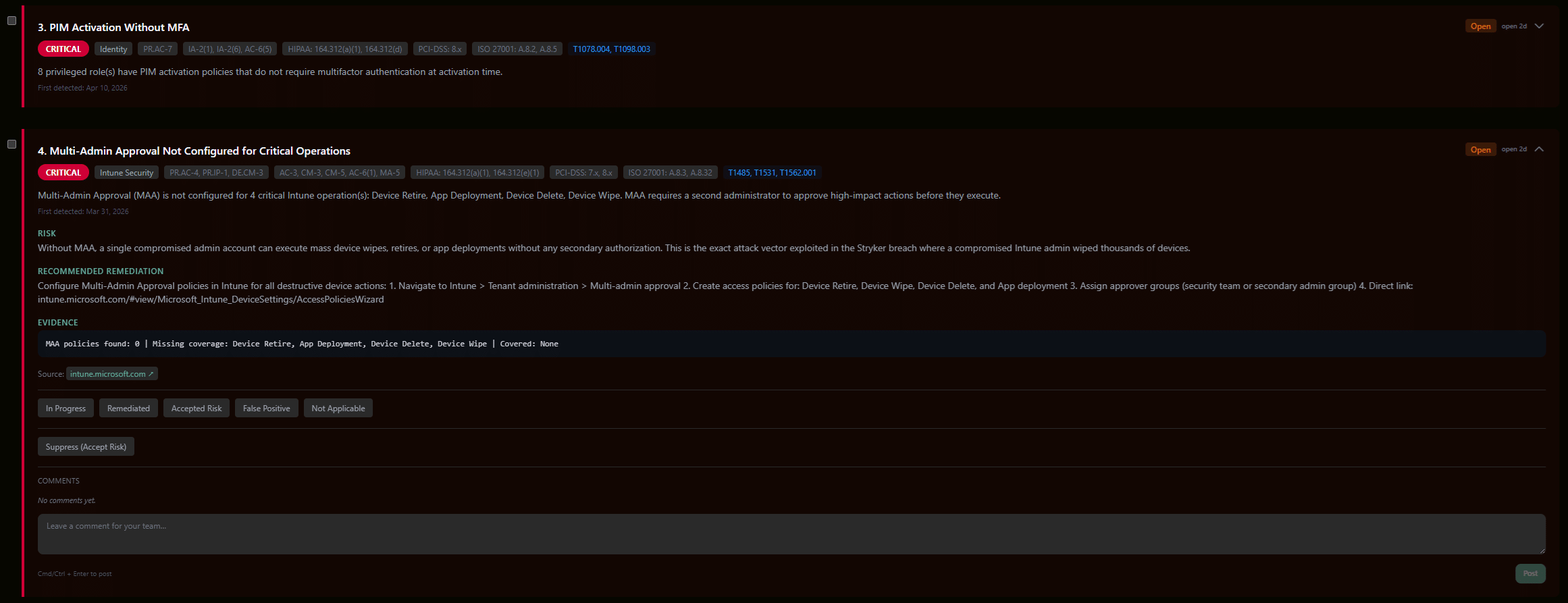
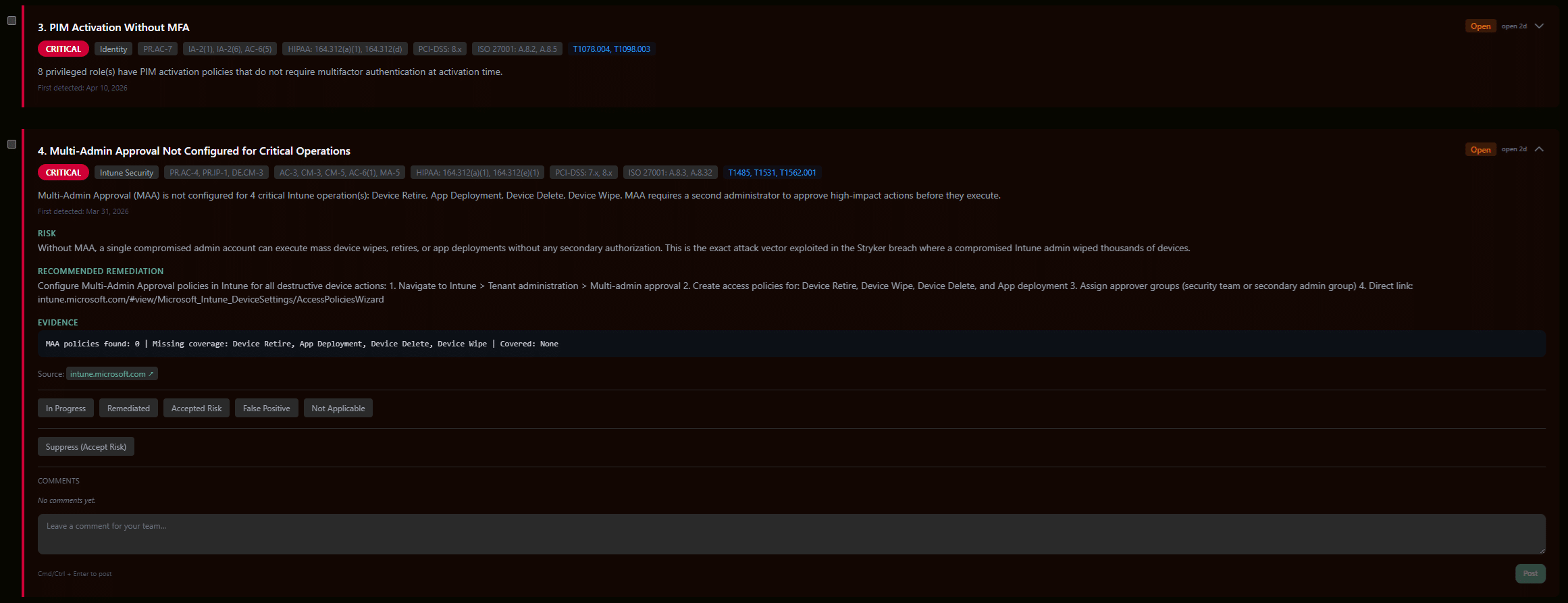
Every finding names the specific account, policy, or role.
Ranked findings tell you what is exposed. The next step is understanding how those findings connect into attack paths an attacker would follow.
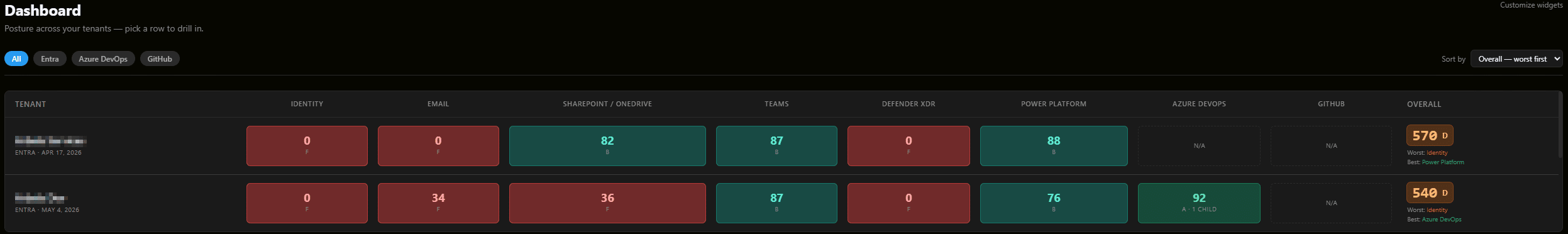
Posture across every tenant, in one view.
Aggregated scores across Identity, Email, SharePoint, Teams, Defender XDR, Power Platform, Azure DevOps, and GitHub. Sort by worst first. Click any score to see the findings behind it.
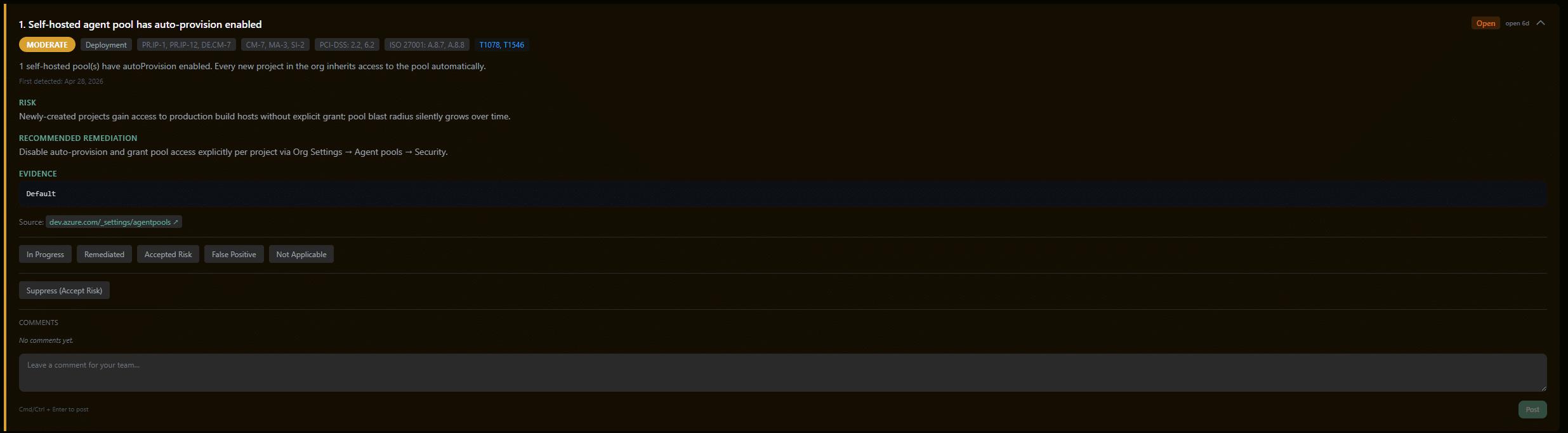
Your deployment pipeline, validated.
GitHub and Azure DevOps scans cover agent pool access, service connections, branch protection, and workflow secrets. Each finding links to its remediation step.
Accelerynt Security Platform Control Validation
Identity
Conditional Access Policies
Coverage gaps, exclusions, and policy drift across your environment.
Identity Controls
MFA enforcement, legacy auth, sign-in risk, account protection.
Privileged Identity
Standing admin rights, PIM coverage, break-glass posture.
Non-Human Identities
Authenticating agents, API connections, and agentic workflows.
Collaboration & Data
Teams & Collaboration
External sharing, guest access, meeting policy, sensitivity labels.
Data Loss Prevention
DLP policy coverage, exceptions, enforcement across workloads.
Exchange Online
Mail flow rules, anti-phishing, impersonation protection, safe links.
Device & Apps
Intune Management
Compliance policies, configuration profiles, enrollment posture.
SharePoint & OneDrive
Sharing boundaries, anonymous links, sync restrictions, retention.
App Registrations
Consent grants, risky permissions, abandoned app identities.
Code & Pipeline
GitHub
Repository permissions, workflow secrets, branch protection, action configurations.
Azure DevOps
Agent pool access, service connections, pipeline policies, deployment controls.
External Attack Surface
DNS & Domains
DMARC, SPF, DKIM, subdomain takeover, domain health.
Asset Timeline
When and where assets are deployed to and removed from the edge. Historic inventory across your external surface.
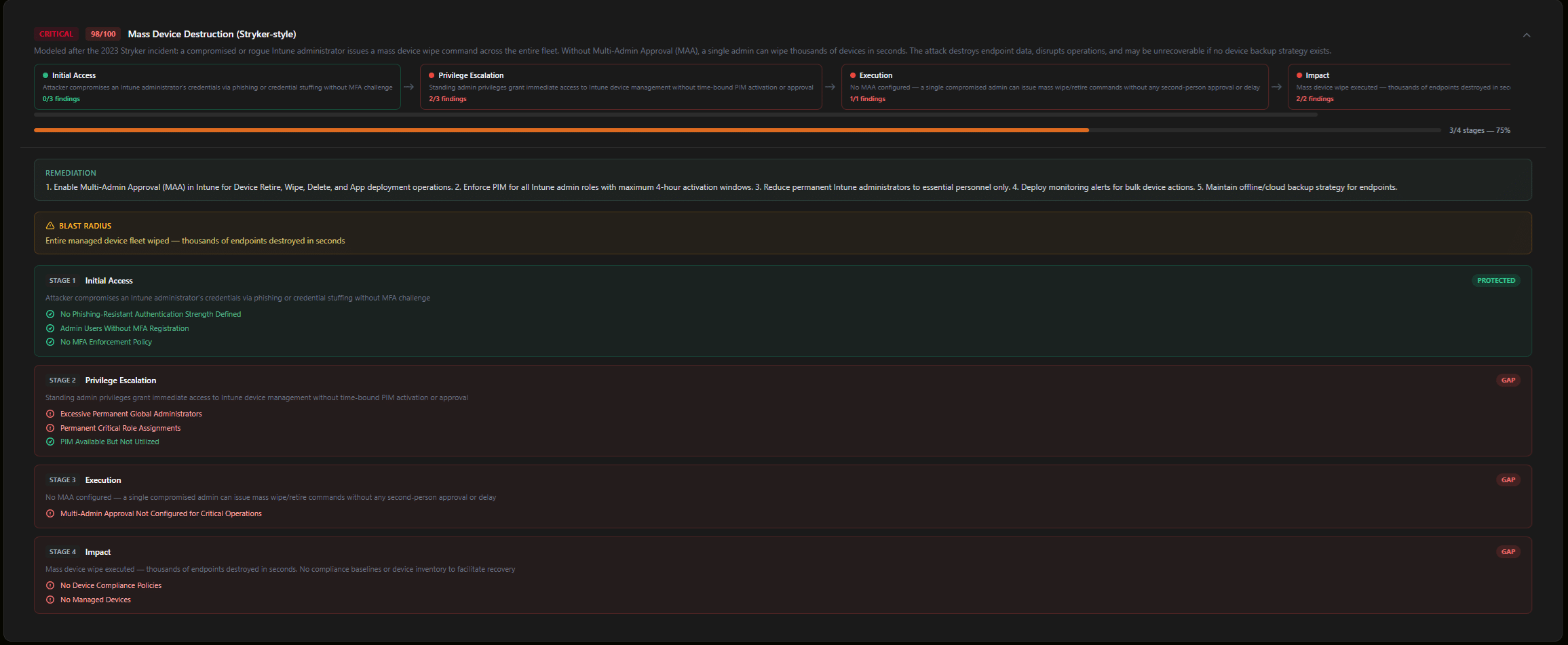
A configuration risk can look minor on its own. Connected into an attack chain, it becomes critical. You see the full path and what to fix first.
See what an attacker would find. Fix it before they exploit it.
Critical vulnerabilities across a complex environment are hard to see. The Accelerynt Security Platform makes them visible and prioritized by risk.
How configuration risks connect.
Your scan findings map to MITRE ATT&CK attack chains specific to your environment. You see how an attacker would move from one finding to the next, and which path to address first.
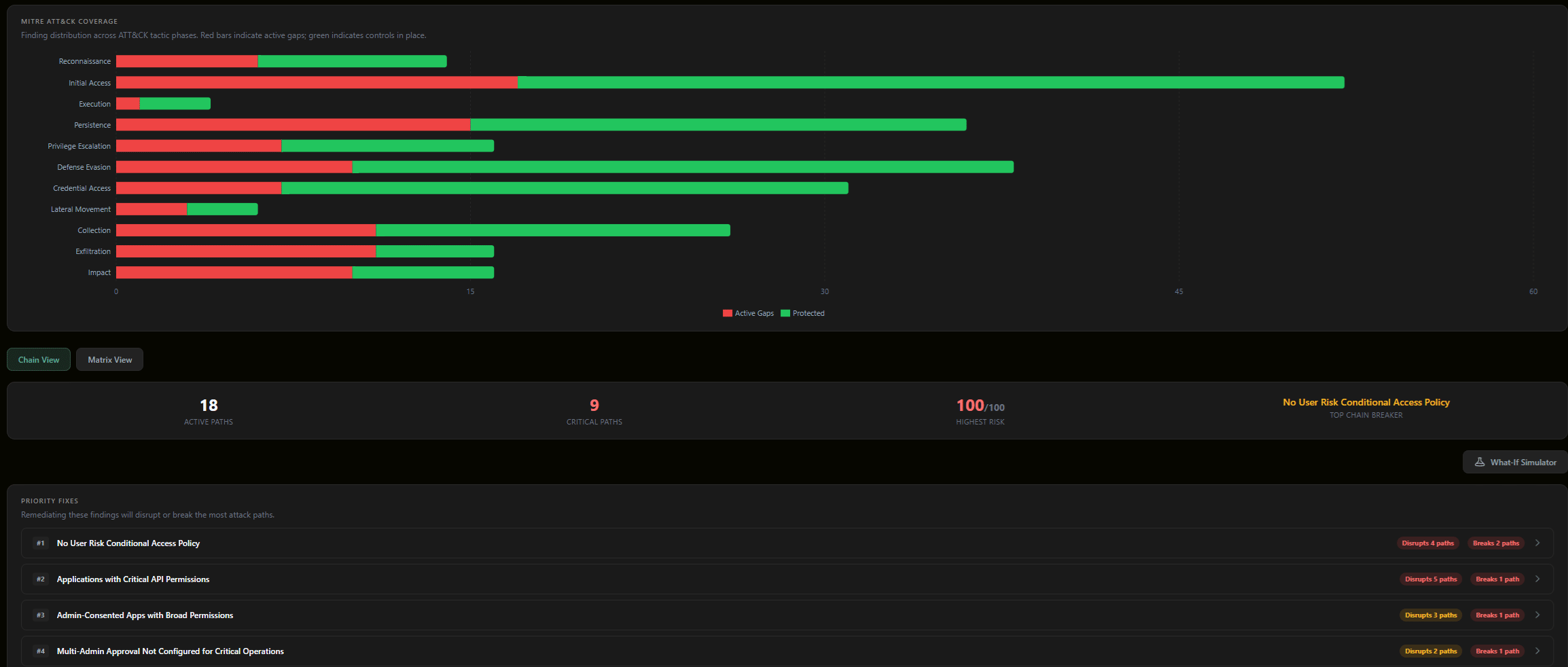
Your technique coverage, measured against MITRE ATT&CK.
The platform maps your scan findings to MITRE ATT&CK techniques and shows catalog coverage as a percentage. You see which techniques your controls address, which remain exposed, and how active attack chains connect across them.
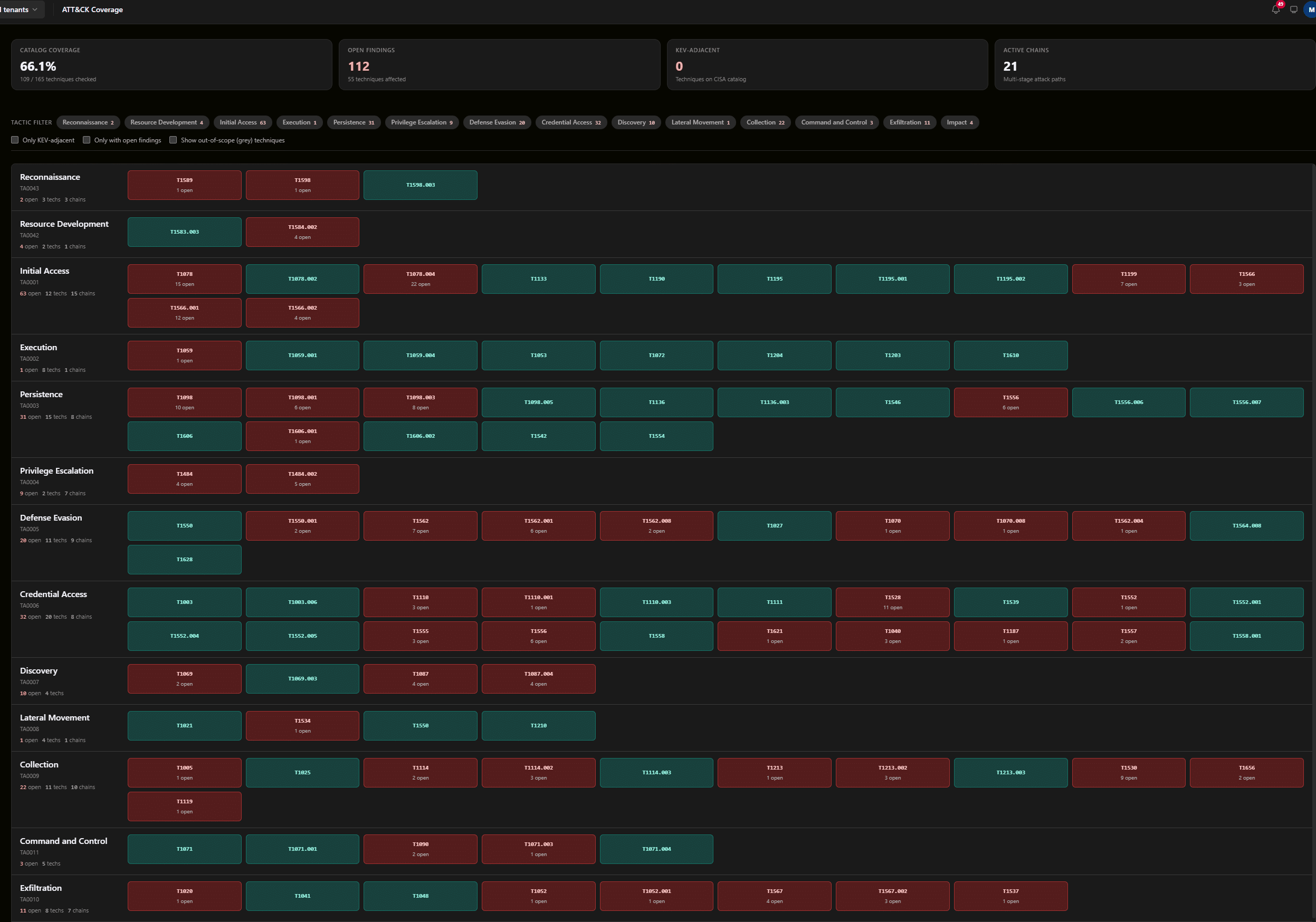
Fix what matters, in the right order.
Chain Breaker™ ranks your fixes by impact. The What-If Simulator™ lets you remove any finding and see which attack chains break before you make the change.
See when a setting changes. Have the proof when someone asks.
When your board, your auditor, or your insurer needs proof of compliance, you already have it.
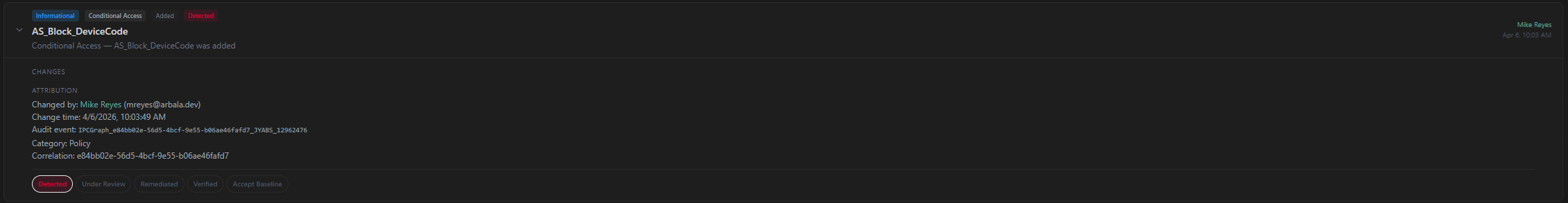
What changed, when, and who changed it.
You see every change with before and after values, when it happened, and the account responsible. Workflow status tracks each event from detection through remediation.
Eight frameworks. One validation pass.
Findings map simultaneously to NIST CSF 2.0, NIST 800-53, MITRE ATT&CK, HIPAA, PCI-DSS v4.0, ISO 27001:2022, CISA SCuBA, and Microsoft MCSB.
An auditable evidence trail generated directly from your own environment.
Proactive Microsoft Security.
Scan in minutes
Full visibility across your Microsoft environment in minutes. Connect once, hit scan, review everything in one place.
See your top risks
You know exactly where to focus. Every finding names the specific account, policy, or role, ranked by what matters most.
See the attacker’s path
Fix what reduces the most risk first. You see how individual findings connect into the paths an attacker would follow.
See what changed
Audit-ready evidence before anyone asks. Every configuration change tracked: what changed, who changed it, and when.
Security validation made easy.
Evidence on demand. Produced from your live environment.